
Today, nearly everything lives online: banking, communication, business data. And the more systems go digital, the greater the number of cyber threats. Hackers target weak systems, outdated software, or careless users. Without strong security and testing, even big organizations can get attacked. That’s why understanding cyber-attacks, and how to prevent them, has become so important. Ethical hackers assist by testing systems before the real attackers strike. They find flaws and help fix them.
Real Attack 1: The 2017 WannaCry ransomware attack
What happened:
In May 2017, the ransomware type of malware named WannaCry spread across hundreds of thousands of computers worldwide. It locked people and companies out of their files, demanding money (a ransom) to unlock them. Many businesses, hospitals, and services were affected.
Why it spread fast:
WannaCry took advantage of a security gap in Windows, a hole for which a patch was already available. But many users and organizations had not updated their systems. Once it infected one computer, malware started spreading fast inside a network.
Impact:
Some of the hospitals had to cancel appointments, businesses suffered data loss, and many users lost access to some very important files. The attack showed just how outdated software and lack of updates could cause big damage.
What we learn:
- Keep the software updated.
- Use strong backups.
- Ethical hacking, also known as penetration testing and vulnerability scanning, identifies those weaknesses before an attacker does.
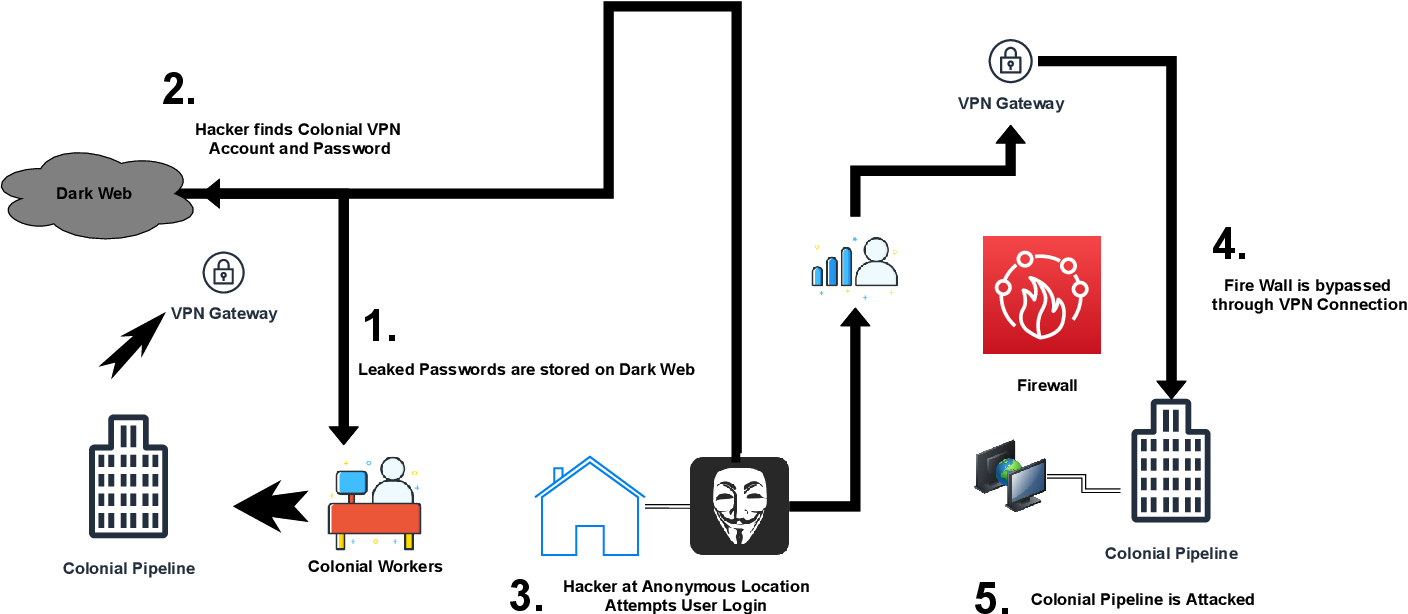
Real Attack 2: The 2021 Colonial Pipeline cyberattack
What happened:
In May 2021, attackers used ransomware on the systems of a major US fuel pipeline company. The effect was the closure of routes for fuel supply across several states. The company paid a ransom to restore the services.
Why it mattered:
This attack disrupted fuel supply, caused panic buying, and showed how cyber attacks can hit not only data, but real-world infrastructure.
What we learn:
- Energy, transport, utilities-all the critical infrastructures are also at risk.
- Security should cover not only the protection of data but also system access control and network monitoring.
- Ethical hacking is important, as are security audits of infrastructure, not just for IT companies.

Recent Big Attacks: Data Breaches & Supply-Chain Hacks
Many attacks do not have the same drama as ransomware nowadays, but they are dangerous in their own right. Hackers break into company servers, pilfer user data (emails, passwords, financial info), or insert malicious code into software libraries – supply-chain attacks.
For example,
- Customer data storage services often get breached due to weak passwords or poor security practices.
- When hackers compromise small software providers, they can affect a great many users at once, even if the target system is large and “secure.”
What we learn:
- Use strong, unique passwords + two-factor authentication (2FA).
- Encrypt sensitive information.
- If you run software or services, do regular security audits and code reviews.
How Ethical Hacking Helps
Ethical hacking, also known as “white-hat hacking” is when security experts attempt to break into a system legally, with permission. They are trying to find weaknesses before the attackers do. They use many of the same techniques that hackers use but report the issues so they can be fixed.
Benefits of ethical hacking and good cyber security:
- Finds weak points before they’re exploited.
- Protects user data and saves companies from embarrassment, legal issues, or financial losses.
- Develop more secure software, networks, and infrastructure.
- Encourages good security habits: Keeping Update, Backup, Password-protecting, and Monitoring.
What You Can Do to Stay Safe
Whether you are an individual or part of a company, here are key steps to protect yourself:
- Always update your software, apps, and operating system when updates become available.
- Use strong, unique passwords, and enable two-factor authentication (2FA) if possible.
- Backup important data regularly (on cloud or external drives).
- Be careful with emails, links, and attachments, don’t click suspicious links (phishing attacks are common).
- If you run a business or website: hire ethical testers or run security audits. Use good encryption and monitor for unusual access.
The Future of Cyber Security
As more devices connect to the internet; phones, smart devices, home systems-so will the cyber threats. Where there’s a new opportunity through emerging technologies, such as cloud computing and AI, comes a new risk. It means ethical hacking and strong cyber defense must keep growing. More investment in security will be made by organizations and governments. Developers will embed safe design practices from day one. Everyday users will learn more about basic protections. This growing awareness and preparedness are going to determine whether we stay safe in a digital world.
Conclusion
From the ransomware chaos caused by WannaCry to the fuel-pipeline disruption caused by Colonial Pipeline, cyber-attacks are serious and real. However, with good cybersecurity practices, awareness, and ethical hacking, we can build strong defenses against them. Everyone has a role to play: companies, governments, and ordinary users. Together, we can make cyberspace safer for all.

